In my previous blog we looked at SharePoint Document Number Generator and SharePoint Bulk Zip & Unzip, which are part of SharePoint Classifier. In this blog we will take a closer look at SharePoint Item Audit Log (which can be purchased separately or also found within our star product, SharePoint Classifier).
Ever wonder who is accessing documents or items from your SharePoint? Do your users have correct permission levels? Are you security conscious and want to secure your documents more efficiently? Is your staff being assigned to much or too little work?

If the answer is yes to all of these questions, then you definitely need to use SharePoint Item Audit Log. This easy to overlook solution will not solve all of the above problems; instead it will generate logs for analysis and give you documentable evidence and information so that you can take the next step in resolving your issues.
Here are some uses for SharePoint Item Audit Log:
- As a gauge to ensure permissions have been granted correctly
- As a security protocol to trace documents that were deleted or restored on your system
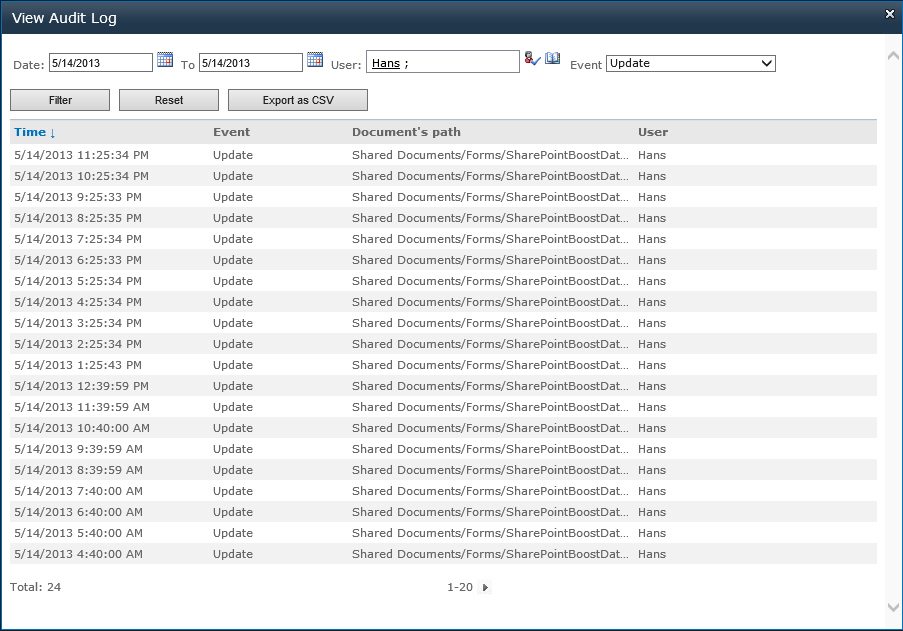
- As a productivity tool to ensure workers are completing assignments on time and are not inundated with work
- To keep track of which documents are being accessed and by whom
- To filter and monitor priority documents and document access
Here are some cases where generating an audit log would be helpful
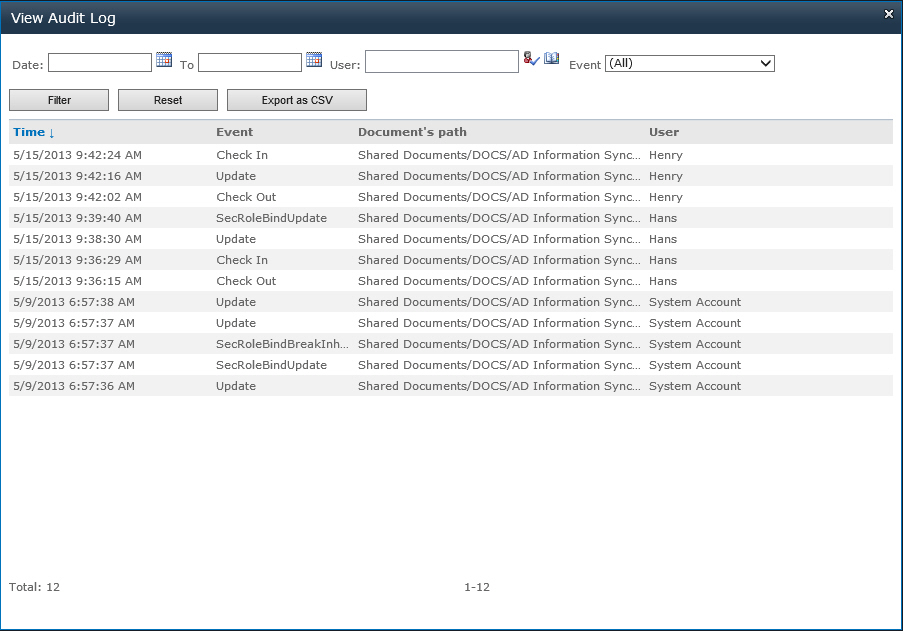
Often permissions may be overlooked or incorrectly given thus users who should not have access to certain libraries or lists may inadvertently be accessing these areas and viewing or changing documents or items. With SharePoint Item Audit Log you can target these users through a simple filtered search and check to see which areas they have been visiting and what documents or items they have been using.
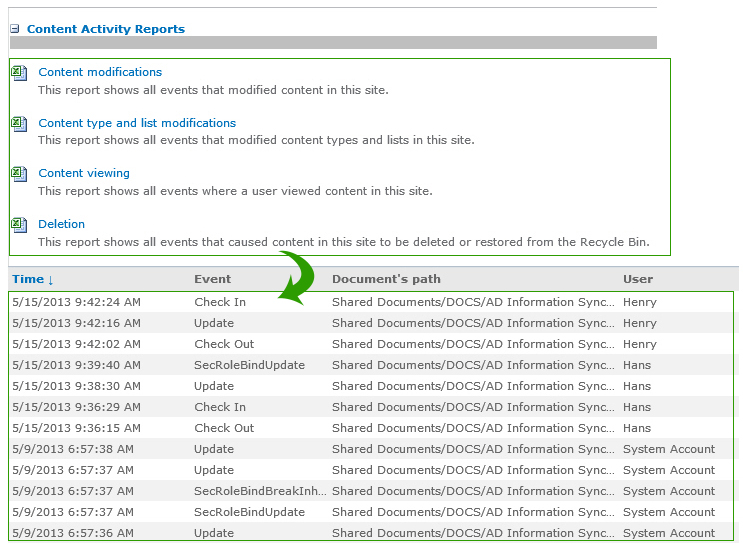
In any organization there is a risk of users accessing libraries or list with sensitive data and using it for their own purposes. SharePoint Item Audit Log gives administrators evidence of user’s activities; libraries and lists they have visited; and documents and items they accessed, changed or removed. With an audit log, organizations can recover their information and instigate security measures to prevent further loss and damage.
Often documents can be deleted by accident or on purpose. These documents can then later be recovered and restored from the recycle bin. With an audit log, administrators can assess if the correct documents have been disposed of or in the case that a document shouldn’t be deleted, to take measures to restore it. Also, if documents have been deleted and need to remain so, administrators can have a record of users who restore it.
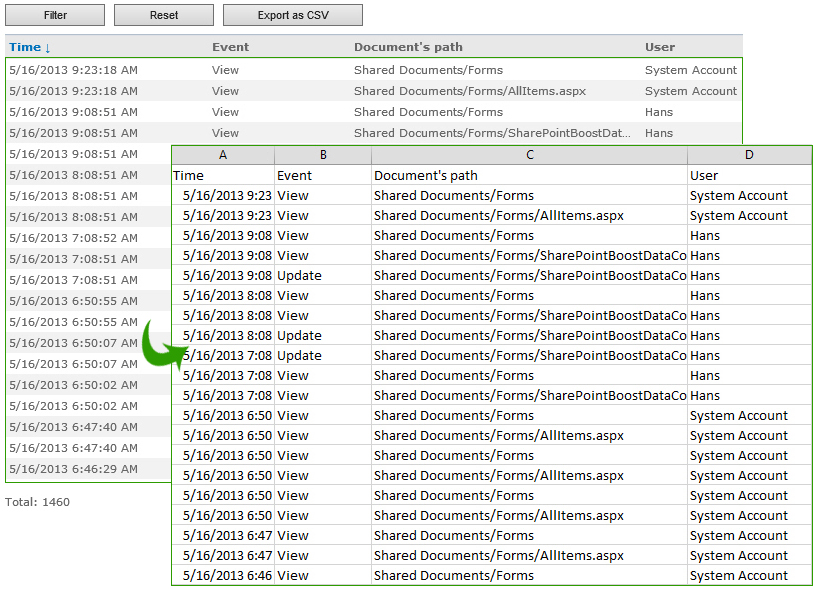
Sometimes there are time-critical or important documents that must be used by everyone or a document must be read by everyone in the company, especially changes in policies or procedures. With SharePoint Item Audit Log administrators can generate an audit log to keep track of critical or important documents; or ensure that a document or item has been accessed by users in an organization.
Please email us if you have any comments or questions: inquiry@boostsolutions.com.






Quick question — can the SharePoint Item Audit Log reports be accessed by users with Edit or Contribute permissions to the site? I have a particular folder (and children) that auditing is turned on for, but using the SharePoint audit logs, only the Site Collection Admins can get the report. I want to be able to give the person that created those folders to be able to pull detailed usage reports without the SC admins having to get involved. Can this be done?