Recently I discovered an interesting thing about SharePoint user management, reusing SharePoint user IDs results in an “Access Denied” error.
This can be replicated using following steps:
- Have user “A” as a SharePoint user.
- Delete user “A” from site collection.
- Delete user “A” from Active Directory.
- Create a new account in AD with the same user “A” name.
- Add user “A” back to SharePoint.
When logging into SharePoint using A’s account, results in an “Access Denied” error. After refreshing AD, restarting IIS, user A’s is still access denied.
Analysis ? I ran a complete test to see what was actually going on:
1. First, I add user “DeleteUser” to a site collection, then I go to Content Database of site collection and open the UserInfo table.
2. I then delete “DeleteUser” from the site collection.
3. I check database again and find that the tp_Deleted column is set to the user’s ID, tp_IsActive column is set to 0 and tp_Token is set to NULL.
4. Everything is normal till now, but then I add a new “DeleteUser” in AD and add it back to SharePoint.
5. However, we can see “DeleteUser” is back with the same data as it had before being deleted.
The Issue:
The reused “DeleteUser” account can no longer access the SharePoint site! If we check the column tp_SystemID for which SID is being used in SharePoint, we find that this SID has not been changed. This is the explanation given by Microsoft: “when you added the user information to SharePoint, SharePoint updated the user’s existing entry in the UserInfo table instead of creating a new entry. However, the user security identifier (SID) in the old entry is no longer correct.” (please refer to kb982949)
Resolution:
I resolved the issue by deleting the “DeleteUser” entry in database and added this user again in SharePoint. However, this is not a very good way, as I have to reassign user’s permissions.
The right way is SharePoint 2010 Management Shell:
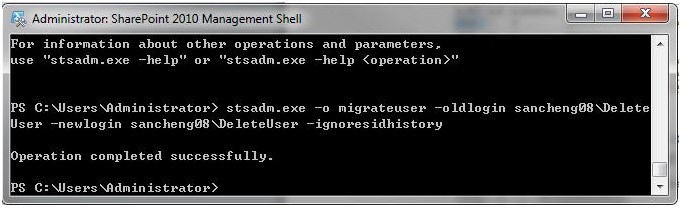
1. On the server that is running SharePoint, open Management Shell and type the following command
stsadm.exe -o migrateuser -oldlogin Domainname\OldUserName -newlogin Domainname\NewUserName ?ignoresidhistory
2. Press the “Enter” button.
3. After running the command, the database entry tp_SystemID changed and DeleteUser can once again logon.
Note: Run this command only from user accounts that are in the same domain. Otherwise, you may experience other permission problems. This command automatically updates the account name and the command maintains the appropriate permissions for the account.










Thanks for posting, very useful.
Thanx man! Really appreciate you guys taking time out to solve our issues. Thanx a lot!
Thanx for this post realy useful!