Guaranteeing list security is usually considered a vital issue for administrators. In this blog, I will give you a brief introduction to the various aspects that will influence list security, so you may take them into consideration when you set list level security settings next time.
A SharePoint farm consists of the following element hierarchy. SharePoint security is managed at every level of the hierarchy.
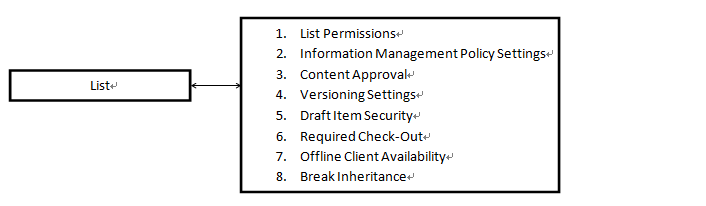
For each layer, the security will be applied differently. Some security is applied at the web application layer, and others are applied as the item layer. The following figure offers an outline of how security is applied on the list layer.
1. List permissions and permission inheritance
The site collection is the security boundary in SharePoint. Permissions within a site collection are inherited from the root site. By default, lists inherit the same permission sets. Permissions can be broken at the list level, so that unique permissions can be set at either level. After a permission is broken, more fine-grained permissions can be defined in that list.
2.Information management policy settings
Information management policy is a set of rules governing the automated management of documents. It enables you to control who has access your information and what they can do with it. In a list or library, you can define a policy to manage how to track and how long to retain documents.
3.Content Approval
Content Approval is an advanced feature that prevents a new item in a list or library from appearing until the item has been approved. When the Content Approval feature is enabled, existing content items will be approved automatically. If Major/Minor versioning is also enabled, then the last major version will automatically be approved, and minor version will be a Draft. In the list, you can select the document from the drop-down menu and “Approve/Reject“ the item. Additionally, you can select the items or documents then click the “Approve/Reject“ ribbon icon.
Note: Items that are in the “Pending state“ can still be viewed by users who have permissions if they have the exact URL to the content item.
4. Versioning settings
Versioning can help administrators prevent losing both data and documents in lists or libraries when the user tries to overwrite the information. With versioning, all changes or updates can be stored as individual versions. When the document is damaged or overwritten incorrectly, the user can just restore from the previous versions.
By requiring documents to be “checked-out” before editing, you can ensure that multiple people do not attempt to upload different local copies of a document, thereby overwriting each other’s changes.
A. Search
Security can involve not only preventing access to a resource by an authenticated user, it can also be used to create barriers that make finding the content more difficult. List setting provides a feature that determines whether or not list items show up in search results. If “No“ is selected, users will not find items in search results. Also, you can find this feature in site settings.
B. Offline Client Availability
This is a new feature for SharePoint 2010. Data loss may happen when people are careless with information security when away from office, or when devices are lost. “Offline Client Availability“ provides a feature to prevent the above cases occurring. If you select “No,” the content cannot be taken offline, thereby limiting access to SharePoint files offline.
Note: Some of the concepts in this blog are quoted or summarized from “Microsoft SharePoint 2010 Administrator’s Companion.“